Professional-Grade Surveillance Tech That Actually Works🔍
Your privacy is under attack. Every day. Everywhere you go. 🚨
Spy gadgets for personal security have evolved from Hollywood fantasy into essential tools for protecting yourself, your family, and your property in our increasingly dangerous world. With hidden cameras smaller than pinhole needles, AI-powered bug detectors that sweep entire rooms in seconds, and night vision systems rivaling military equipment, professional surveillance technology is no longer exclusive to secret agents and government operatives.
The harsh reality? 11% of travelers will be exposed to hidden cameras this year alone. From Airbnb hosts secretly recording guests to corporate competitors planting listening devices, surveillance threats lurk everywhere. But here’s the game-changer: the same advanced technology being used against you is now available for your protection at prices that won’t break the bank.
The global security camera market exploded to $43.65 billion in 2024 and is projected to reach $81.37 billion by 2030 – that’s 11.2% annual growth driven by skyrocketing demand for personal protection technology. Meanwhile, the spy camera market alone hit $1.25 billion in 2023 and is racing toward $2.45 billion by 2032. This isn’t just market growth – it’s a revolution in personal security accessibility.
The Hidden Camera Revolution: Eyes Everywhere, Protection Everywhere 👁️
Hidden cameras have transformed from expensive spy movie props into affordable protection tools that can safeguard your most precious assets. Modern surveillance cameras are so sophisticated they make James Bond’s gadgets look like children’s toys, yet they’re simple enough for anyone to use effectively.
Everyday Object Cameras: The Ultimate Stealth Technology
The most effective hidden cameras are the ones nobody suspects. Today’s spy gadgets for personal security are built into fully functional everyday objects that actually work as intended while secretly recording everything in crystal-clear 4K resolution.
Smoke Detector Cameras remain the gold standard for home surveillance. These aren’t fake smoke detectors – they actually detect smoke and function as legitimate safety devices while housing sophisticated 4K cameras with infrared night vision. The built-in WiFi enables remote viewing from anywhere in the world, motion detection ensures you only capture relevant footage, and installation is as simple as replacing your existing smoke detector. Professional models offer 30-day standby time and can store weeks of footage.
USB Charger Cameras represent the pinnacle of portable surveillance technology. These fully functional phone chargers contain tiny cameras recording in 1080p HD while simultaneously charging your devices. Perfect for hotel rooms, offices, conference rooms, or anywhere you need discrete monitoring without arousing suspicion. Advanced models include voice activation, night vision, and can stream live footage directly to your smartphone. The beauty lies in their perfect camouflage – everyone expects to see phone chargers everywhere.
Clock Radio Cameras provide 24/7 surveillance disguised as bedroom or office essentials. Modern models include genuine AM/FM radio functionality, dual USB charging ports, and hidden cameras with infrared night vision capabilities. The timestamp feature helps with evidence collection, and remote viewing means you can monitor your space from anywhere. Some advanced models can record continuously for up to 30 days while maintaining full clock functionality.
Picture Frame Cameras offer domestic surveillance that’s completely invisible. These aren’t fake frames – they display actual rotating photos while housing sophisticated recording equipment. Motion activation preserves battery life, live streaming capabilities allow real-time monitoring, and the natural placement in homes and offices makes them virtually undetectable.
Just like how smart home technology has revolutionized how we interact with our living spaces, hidden surveillance technology is transforming personal security by making professional-grade protection accessible and invisible.
Professional-Grade Miniaturization: Big Protection, Tiny Package
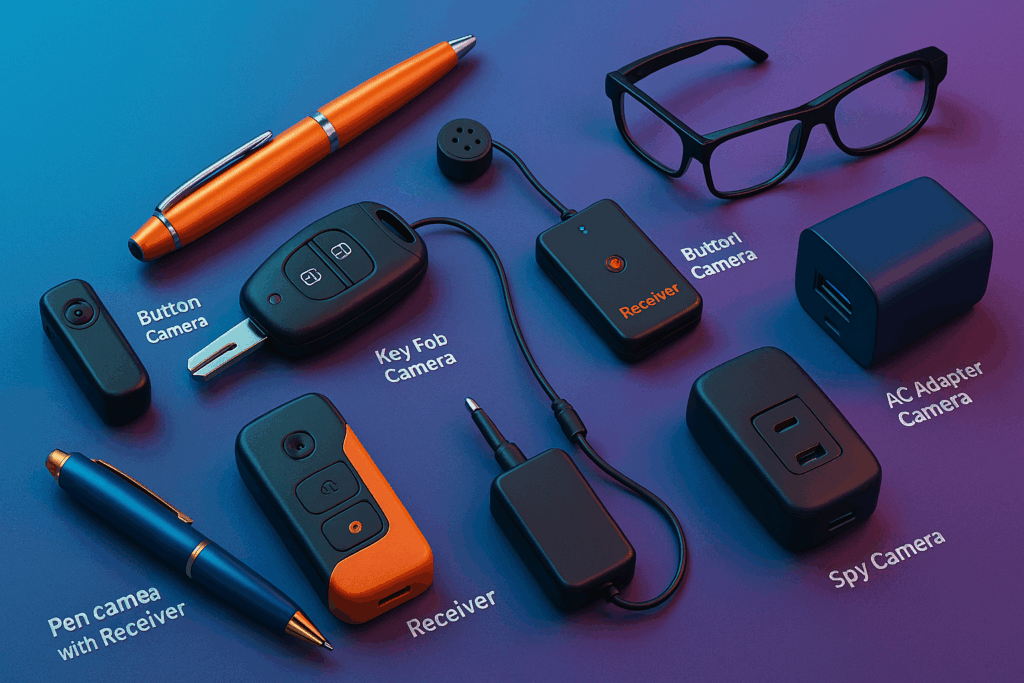
Pen cameras showcase the incredible advancement in surveillance miniaturization. These aren’t toy gadgets – professional pen cameras feature 2.8mm wide-angle cameras, microSD card slots, built-in microphones, and record in genuine 4K resolution. The latest models offer up to 2 hours continuous recording and look identical to high-end writing instruments. Perfect for documenting workplace harassment, recording important business meetings, or gathering evidence in sensitive legal situations.
Button cameras push miniaturization to the absolute limit. These microscopic devices, barely larger than shirt buttons, capture 1080p video while remaining completely invisible during normal interactions. Professional models feature twist-lock security connections preventing accidental disconnection and can record for up to 3 hours on a single charge. Law enforcement and private investigators rely on these devices for undercover operations and evidence gathering.
Smart glasses with integrated cameras provide hands-free recording capabilities without compromising natural appearance. Modern spy glasses look identical to regular prescription eyewear or stylish sunglasses while housing tiny cameras capable of recording both video and audio. Perfect for journalists conducting investigative interviews, professionals documenting workplace issues, or anyone needing to record interactions without alerting others.
The sophistication of these devices mirrors advances in smartphone technology, where incredible capabilities are packed into increasingly smaller form factors.
The Counter-Surveillance Arms Race: Detecting Hidden Threats Before They Hurt You 🛡️
Someone might already be watching you. Hidden cameras, listening devices, and GPS trackers are more common than most people realize, but detection technology has evolved to match surveillance sophistication. Professional counter-surveillance equipment can identify threats in minutes and protect your privacy before it’s violated.
Advanced RF Bug Detection Systems
Professional RF detectors represent the front line of personal privacy protection. Modern devices like the JMDHKK M8000 AI RF Detector use artificial intelligence to distinguish between legitimate devices (your WiFi router, smartphone, smart TV) and potential surveillance threats. These sophisticated systems can identify:
- Audio bugs and hidden listening devices
- WiFi cameras and wireless IP cameras
- GSM bugs and cellular phone taps
- GPS trackers (both active and dormant modes)
- Body wires and concealed microphones
- Bluetooth surveillance devices
Frequency range capabilities matter enormously. Professional detectors sweep from 1MHz to 8GHz, covering virtually all surveillance devices including the latest digital systems. Budget detectors often miss modern sophisticated bugs operating on specific encrypted frequencies, leaving you vulnerable to high-tech surveillance threats.
AI-enhanced detection algorithms eliminate false positives by learning your environment’s normal electronic signature. These systems can differentiate between your legitimate devices and foreign surveillance equipment, dramatically improving detection accuracy while reducing annoying false alarms.
Camera Detection Technology: Finding Hidden Eyes
Lens detection remains the most reliable method for finding concealed cameras regardless of whether they’re powered on or streaming. Professional detection devices use bright infrared LED arrays combined with specialized optical filters that make camera lenses appear as distinctive bright reflections.
The detection process is surprisingly simple yet incredibly effective: scan rooms slowly with the detector while looking through the viewfinder. Any camera lens – whether hidden in smoke detectors, clocks, picture frames, or even tiny pinhole cameras – creates unmistakable bright reflections visible only through the detector’s filter.
Advanced detection models include multiple infrared frequency ranges to catch different types of camera lenses, adjustable sensitivity levels for various room sizes, and vibration alerts for silent operation. Professional models can detect camera lenses from across large rooms and distinguish between camera reflections and harmless reflective surfaces like mirrors or chrome fixtures.
The importance of detection technology parallels cybersecurity protection – you need to actively defend against threats rather than hoping they’ll never target you.
GPS Tracker Detection: Stopping Location Stalking
GPS tracking has become the most common surveillance method used by stalkers, suspicious partners, private investigators, and corporate competitors. Modern GPS trackers are incredibly small – some no bigger than matchboxes – yet can operate for weeks or months on single battery charges while providing real-time location data.
Magnetic field detection proves crucial because most vehicle GPS trackers use powerful magnets for quick, secure attachment. Professional detectors include telescoping magnetic probes reaching into wheel wells, under bumpers, inside engine compartments, and other hard-to-access hiding spots where trackers are commonly placed.
Active tracking detection identifies GPS devices currently transmitting location data. These devices typically send position updates every 10-30 seconds to remote tracking servers. Professional detectors recognize these transmission patterns and alert you to active surveillance, often pinpointing the tracker’s exact location.
Comprehensive sweep procedures should include both magnetic detection and RF signal analysis. Some advanced trackers use non-magnetic mounting methods or operate in low-power modes that only transmit occasionally, requiring sophisticated detection methods to identify them.
Night Vision and Thermal Imaging: Seeing What Others Cannot 🌙
Professional night vision technology has transitioned from military-exclusive equipment to civilian personal security tools. Modern night vision and thermal imaging devices provide incredible tactical advantages for property protection, search operations, and personal safety that were unimaginable just years ago.
Digital Night Vision: Clarity in Complete Darkness
Digital night vision has revolutionized civilian surveillance by offering several key advantages over traditional analog systems. Digital devices capture infrared light and display results on high-resolution screens, enabling video recording, photo capture, wireless streaming, and smartphone integration.
Professional digital night vision advantages:
- Records HD video and photos for evidence documentation
- Significantly more affordable than military analog systems
- Functions with built-in IR illuminators for complete darkness operation
- Allows live streaming to smartphones for remote monitoring
- More durable and weather-resistant than delicate analog tubes
- Hands-free operation through headmountable designs
Leading systems like professional Nightfox devices offer both handheld flexibility for targeted surveillance and headmountable designs allowing users to maintain full mobility while monitoring their environment. Advanced models include GPS tracking, compass functionality, and can operate effectively in various weather conditions.
Thermal Imaging: The Ultimate Detection Advantage
Thermal imaging detects heat signatures rather than reflected light, making it effective in complete darkness, through light vegetation, fog, and even some weather conditions that defeat traditional cameras. Modern handheld thermal cameras can detect human body heat from hundreds of yards away.
Thermal imaging provides unique capabilities:
- Functions in complete darkness without any illumination
- Detects people hiding behind light cover or camouflage
- Identifies recent human activity through heat footprints
- Cannot be countered by traditional hiding methods
- Effective through fog, light rain, dust, and smoke
- Reveals temperature differences indicating equipment problems
Professional thermal monoculars now cost under $2,000 for quality resolution models, making this formerly military-exclusive technology accessible for serious personal security applications. Advanced fusion systems combine thermal and traditional night vision for ultimate surveillance capability.
The integration of multiple detection technologies mirrors how advanced tech gadgets combine various functions to provide comprehensive solutions.
GPS Tracking Technology: Protection and Location Intelligence 🗺️
GPS tracking serves both offensive and defensive security purposes in personal protection scenarios. While GPS trackers can be misused for unauthorized surveillance, they’re also invaluable tools for protecting vehicles, valuable assets, elderly family members, and even monitoring teenage drivers for safety.
Vehicle Protection and Recovery Systems
Professional vehicle tracking systems extend far beyond simple location monitoring. Modern systems integrate sophisticated smartphone applications providing comprehensive vehicle security:
- Real-time location tracking with minute-by-minute position updates
- Geofencing alerts when vehicles enter or leave designated safe areas
- Speed monitoring and aggressive driving behavior alerts
- Battery voltage monitoring preventing unexpected dead battery situations
- Tamper detection alerts if tracking devices are discovered or disturbed
- Historical route tracking for investigating suspicious vehicle usage
Covert installation proves crucial for effective vehicle tracking systems. Professional installers can conceal trackers in dozens of locations throughout vehicles, making discovery nearly impossible without specialized detection equipment. Popular hiding spots include inside bumpers, wheel wells, under spare tires, and within electronic system housings.
Asset Protection and Recovery Technology
High-value asset tracking has become essential for protecting expensive equipment, artwork, jewelry, collectibles, and other portable valuables. Modern tracking devices are smaller than credit cards while offering extended battery life measured in months rather than days.
Advanced tracking features include:
- Motion-activated operation preserving battery life
- Waterproof construction for outdoor and marine use
- International roaming capabilities for travel protection
- Multiple communication methods (GPS, cellular, WiFi, Bluetooth)
- Panic button functionality for personal emergency situations
- Historical tracking data for investigating theft or unauthorized use
Smart integration with existing security systems amplifies protection effectiveness. Modern trackers can trigger security cameras, send emergency alerts to multiple contacts, and integrate with smart home systems for comprehensive property protection.
Audio Surveillance: The Invisible Intelligence Network 🎧
Audio surveillance remains one of the most powerful yet underutilized personal security technologies. Modern listening devices offer crystal-clear audio capture, intelligent noise filtering, voice activation, and remote monitoring capabilities that can capture crucial evidence in legal, professional, and personal protection scenarios.
Professional Voice Recording Systems
Digital voice recorders have evolved far beyond simple handheld devices. Professional surveillance-grade systems offer game-changing capabilities:
- Voice-activated recording preserving storage space and battery life
- Advanced noise reduction and audio enhancement technology
- Precise timestamping for legal evidence requirements
- Remote activation and live monitoring capabilities
- Extended battery life measured in weeks for long-term operations
- Smartphone integration for instant audio streaming and alerts
Smartphone connectivity enables many modern voice recorders to stream live audio directly to your phone, providing real-time monitoring capabilities from anywhere worldwide. This technology proves invaluable for monitoring elderly relatives, tracking children’s safety, or documenting workplace harassment.
Wearable Audio Surveillance Technology
Body-worn recording devices offer discrete audio capture during personal interactions. Modern wearable recorders disguised as fitness trackers, key fobs, or clothing accessories can record for hours while remaining completely undetectable.
Popular wearable formats include:
- Fitness tracker recording devices with genuine activity monitoring functions
- Keychain recorders perfect for vehicle surveillance or mobile operations
- Button recorders that integrate seamlessly with business attire
- Power bank recorders offering extended recording time while charging devices
- Pen recorders combining writing functionality with high-quality audio capture
Counter-Audio Security: Protecting Your Conversations
Audio jamming devices create protective privacy bubbles by generating targeted white noise preventing microphones from recording clear audio. Modern jammers represent sophisticated counter-surveillance technology:
- Multiple noise pattern generation countering different recording technologies
- Automatic output adjustment based on environmental acoustic conditions
- Silent operation while effectively blocking surveillance attempts
- Portable privacy protection for sensitive business or personal conversations
- Integration with mobile apps for remote activation and control
The need for audio privacy protection has grown as dramatically as online privacy concerns in our constantly-monitored digital world.
Smart Detection Systems: AI-Powered Personal Security Revolution 🤖
Artificial intelligence has fundamentally transformed personal security technology by enabling devices to distinguish between legitimate activity and genuine threats. Modern AI-powered security systems learn your behavioral patterns and alert you only to truly suspicious activities, dramatically reducing false alarms while ensuring real threats never go unnoticed.
Intelligent Camera Systems and Analytics
AI-powered surveillance cameras differentiate between humans, animals, vehicles, and inanimate objects with remarkable accuracy. This dramatically reduces false alarms while ensuring important security events are never missed. Advanced systems include facial recognition capabilities that can identify specific individuals and send customized alerts for unwanted visitors.
Behavioral analysis technology identifies suspicious activity patterns including loitering, unusual movement sequences, attempts to avoid camera coverage, or aggressive gestures. These systems continuously learn what normal activity looks like in your environment and flag significant deviations for immediate review.
Professional AI features include:
- Person and vehicle recognition with customizable alert settings
- Crowd behavior analysis for unusual gathering patterns
- Abandoned object detection for potential security threats
- Perimeter breach detection with intelligent zone monitoring
- Integration with access control systems for comprehensive security
Automated Threat Detection Networks
Professional AI security systems integrate multiple sensor types creating comprehensive threat detection networks that respond intelligently to various security scenarios:
- Motion sensors with advanced pet-immune technology eliminating false alarms
- Glass break detectors with acoustic signature analysis
- Door and window sensors with sophisticated tamper detection
- Environmental sensors monitoring smoke, carbon monoxide, flooding, and temperature
- Vibration sensors detecting attempts to breach walls or barriers
Smartphone integration provides instant notifications with video clips, remote system control, live camera feeds, and two-way communication with visitors or intruders. Modern systems allow complete remote management from anywhere worldwide while maintaining local operation during internet outages.
The sophistication of modern security AI parallels advances in artificial intelligence tools that make complex technology accessible to everyday users.
Communication Security: Protecting Your Most Sensitive Information 📱
Every conversation is potentially monitored in our hyper-connected world. Professional-grade communication security tools protect your most sensitive discussions from interception, eavesdropping, and unauthorized surveillance using military-grade encryption and signal blocking technology.
Encrypted Communication Systems
Military-grade encryption has become available in consumer communication devices, providing secure channels for sensitive conversations. Encrypted radios, satellite communicators, and secure messaging systems ensure communications remain private even under sophisticated surveillance attempts.
Professional communication security features:
- End-to-end encryption preventing signal interception and decoding
- Frequency hopping technology preventing signal jamming attempts
- Burst transmission modes minimizing detection opportunities
- Emergency beacon capabilities for crisis situation communication
- Mesh networking allowing communication when traditional networks fail
Signal Blocking and Privacy Protection
Faraday bag technology blocks all radio signals, ensuring devices cannot be tracked, hacked, monitored, or remotely accessed when privacy is essential. Professional Faraday bags protect multiple device types simultaneously:
- Smartphones and tablets from remote hacking and location tracking
- Credit cards and passports from RFID skimming and data theft
- Key fobs from signal cloning and vehicle theft attempts
- Laptops and storage devices from electromagnetic interference
- Digital cameras and recording devices from remote access attempts
Advanced Faraday protection includes multiple shielding layers, military-grade construction, and testing certification ensuring complete signal blocking across all frequency ranges. Some models include viewing windows allowing device use while maintaining protection.
Privacy protection complexity mirrors password security management – comprehensive protection requires multiple layers and systematic approach.
Legal Framework: Navigating Surveillance Laws Without Getting Arrested ⚖️
Understanding legal boundaries is absolutely critical before purchasing or using surveillance equipment. Surveillance laws vary dramatically by jurisdiction, and violations can result in serious criminal charges, substantial civil liability, equipment confiscation, and even federal prosecution in extreme cases.
Federal Privacy Protections
Federal wiretapping laws under the Electronic Communications Privacy Act (ECPA) specifically address interception of oral communications. Federal privacy laws clearly dictate that security cameras (both visible and hidden) cannot be placed in areas with reasonable expectation of privacy including bathrooms, changing rooms, bedrooms, or private offices.
Key federal principles:
- Fourth Amendment protections against unreasonable searches and seizures
- Reasonable expectation of privacy standards protecting private spaces
- Interstate surveillance requiring additional federal compliance
- Commercial surveillance subject to business privacy regulations
State-by-State Recording Laws
State laws create the primary legal framework for surveillance activity, with dramatic variations in requirements and restrictions:
One-party consent states (including Texas and New York) allow recording when one participant knows about it. You can record conversations you’re part of without informing other parties.
All-party consent states require everyone involved to consent to recording, making covert audio surveillance significantly more challenging and legally risky.
Specific state restrictions:
- California prohibits recording confidential communications
- Florida allows hidden video in non-private settings
- Georgia requires visible camera placement in most situations
- Minnesota restricts consent requirements for private space recording
Workplace Surveillance Regulations
Employment law creates additional legal complications for surveillance technology. While employers generally have broad rights monitoring workplace activity, employees retain privacy protections in personal spaces like break rooms, bathrooms, and changing areas.
Professional workplace considerations:
- Company policies may explicitly prohibit personal recording devices
- Union contracts may restrict surveillance activities and data collection
- Industry-specific regulations may limit recording capabilities
- Professional licenses may be affected by surveillance law violations
- Evidence admissibility requires legal compliance during collection
Best Practices for Legal Compliance
Documentation and transparency provide your best legal protection when using surveillance equipment within legal boundaries:
- Maintain detailed records documenting when and why you’re conducting surveillance
- Post appropriate legal notices when required by local or state law
- Consult qualified legal counsel for complex or high-stakes situations
- Focus on protecting yourself rather than gathering intelligence on others
- Respect others’ reasonable privacy expectations even when technically legal
Legal compliance for surveillance mirrors cybersecurity best practices – proactive protection and systematic approach prevent serious problems.
Market Analysis: The Explosive Growth of Personal Protection Technology 📈
The personal security market is experiencing unprecedented expansion driven by increasing crime rates, growing privacy concerns, technological advancement, and democratization of professional surveillance equipment. Understanding market trends helps identify the most effective and future-proof security technology investments.
Market Size and Explosive Growth Projections
The global surveillance camera market reached $43.65 billion in 2024 and is projected to grow at 11.2% annually, reaching $81.37 billion by 2030. The spy camera market specifically exploded from $1.25 billion in 2023 toward an expected $2.45 billion by 2032, representing sustained 7.5% compound annual growth.
Key market growth drivers:
- Rising residential and commercial break-in rates driving security demand
- Increased awareness of sophisticated surveillance threats requiring counter-measures
- Technological advances making professional equipment affordable for consumers
- Growing demand for remote monitoring capabilities during travel and work
- Integration with smartphone technology making systems user-friendly
Regional market leadership:
- Asia Pacific dominates with 58.2% global market share in 2024
- North America shows 32% market share with premium pricing
- European markets emphasize privacy-compliant technology solutions
- Emerging markets focus on affordable basic security implementations
Technology Convergence and Innovation Trends
Convergence of multiple technologies creates increasingly powerful and versatile security systems combining previously separate capabilities:
- High-definition video recording with automatic cloud backup storage
- AI-powered threat detection with instant smartphone alert systems
- GPS tracking integration with geofencing and automated response capabilities
- Voice recognition systems with automated threat response protocols
- Thermal imaging combined with traditional night vision systems
Consumer adoption patterns show dramatic shift toward DIY security systems as consumers seek affordable alternatives to expensive professional monitoring services while maintaining direct control over their security infrastructure and data.
The security market’s evolution reflects broader trends in consumer technology adoption where early adopters drive innovation while mainstream users benefit from mature, proven solutions.
Professional vs Consumer Grade: Understanding Critical Differences 🎯
Quality differences between professional and consumer surveillance equipment can mean the difference between capturing usable evidence and having worthless footage when you need it most. Understanding these distinctions proves crucial for making informed purchasing decisions and setting realistic performance expectations.
Image and Audio Quality: Evidence-Grade vs Convenience
Professional surveillance equipment prioritizes evidence quality over user convenience features. Professional cameras record in higher resolutions, use superior sensors for low-light performance, include advanced stabilization systems, and offer optical zoom capabilities maintaining image quality.
Consumer devices emphasize ease of use and smartphone integration, sometimes sacrificing critical image quality for convenient features like wireless connectivity, compact size, extended battery life, and simple mobile app control.
Quality comparison factors:
- Sensor size and low-light performance capabilities
- Optical vs digital zoom maintaining image sharpness
- Image stabilization for clear footage during movement
- Audio quality and noise reduction for evidence purposes
- Weather resistance for outdoor surveillance applications
Durability and Operational Reliability
Professional equipment builds for continuous operation under challenging environmental conditions. Military-specification construction, extended temperature operation ranges, shock resistance, and robust mechanical designs ensure reliable operation during critical security situations.
Consumer devices typically prioritize cost and convenience over extreme durability, making them suitable for occasional use but potentially unreliable for critical long-term security applications where failure isn’t acceptable.
Detection Resistance and Counter-Surveillance Features
Professional surveillance equipment often includes sophisticated counter-detection features like infrared-blocking materials, RF signal shielding, non-reflective lens coatings, and frequency randomization. These features make devices much harder to detect using consumer-grade detection equipment.
Consumer spy gadgets rarely include counter-detection capabilities, making them vulnerable to discovery by even basic detection equipment. This limitation could compromise security operations or alert targets to surveillance activities.
The choice between professional and consumer equipment requires the same careful analysis as selecting appropriate cloud computing solutions based on actual requirements versus desired features.
Building Your Personal Security Arsenal: Strategic Defense Planning 🛡️
Creating an effective personal security system requires strategic thinking rather than random gadget accumulation. The most successful security implementations layer multiple complementary technologies creating comprehensive coverage while remaining affordable and manageable for long-term operation.
Threat Assessment and Security Planning
Professional security planning begins with comprehensive threat assessment identifying your specific vulnerabilities and protection requirements:
- Asset identification: What are you protecting? (family, property, information, business assets)
- Threat analysis: Who represents potential threats? (strangers, known individuals, competitors, ex-partners)
- Vulnerability mapping: What are your security weak points? (entry points, blind spots, predictable routines)
- Resource allocation: What capabilities do you have? (budget constraints, technical skills, time availability)
Priority ranking focuses spending on most critical security needs first. Protecting against likely threats with serious consequences should take precedence over exotic scenarios with minimal probability or impact.
Foundation Security Technology Implementation
Every personal security system should establish basic coverage before expanding into specialized applications:
Hidden camera systems provide visual evidence and psychological deterrent effects. Start with one high-quality camera covering your most valuable or vulnerable area, then systematically expand coverage as budget and experience allow.
Detection equipment ensures you’re not being surveilled by hostile parties. Quality RF detectors and camera finders should rank among your first purchases, as they protect all other security investments from compromise.
Communication security protects your planning and emergency response capabilities. Secure communication methods ensure threats cannot monitor your security activities, response plans, or coordinate counter-surveillance against your systems.
Advanced Integration and Automation Strategies
Layered security systems multiply protection effectiveness by combining multiple technologies covering each other’s limitations:
- Cameras provide visual evidence but can be avoided, disabled, or blocked
- Motion sensors cover areas cameras miss but may generate false alarms
- Audio recording captures evidence visual systems might miss completely
- Access control limits entry points but requires backup detection systems
- Communication systems ensure help can be summoned when other systems detect threats
Centralized smartphone integration simplifies system management while providing remote monitoring capabilities. Modern security applications allow monitoring multiple systems simultaneously, receiving filtered intelligent alerts, and responding to threats from anywhere worldwide.
The systematic approach required resembles comprehensive IT infrastructure planning where multiple technologies must work together seamlessly.
Installation and Deployment: Making Professional Technology Work 🔧
Even the most advanced security equipment proves useless if improperly installed or configured. Professional deployment requires understanding both technical specifications and practical operational requirements while maintaining covert operation and legal compliance.
Site Survey and Strategic Planning
Professional installation begins with thorough environmental analysis:
- Coverage area mapping: Identify all spaces requiring surveillance or protection
- Power source planning: Locate reliable power sources and plan battery backup systems
- Communication infrastructure: Ensure stable network connectivity for remote monitoring
- Concealment opportunities: Identify natural hiding places maintaining device effectiveness
- Access control planning: Secure maintenance access while preventing unauthorized tampering
Environmental factors including lighting conditions, weather exposure, traffic patterns, and potential interference sources must be carefully evaluated during planning phases.
Professional Installation Standards
Hidden cameras require precise positioning maximizing coverage while maintaining complete concealment:
- Optimal height and angle positioning avoiding backlighting while maximizing facial recognition
- Power management planning for extended operation periods with minimal maintenance
- Network security implementation securing wireless connections preventing hacking or interception
- Storage management configuration with automatic archiving for important footage preservation
Detection equipment deployment requires systematic positioning for maximum threat identification effectiveness:
- Comprehensive search pattern development ensuring complete area coverage during sweeps
- Regular calibration and testing maintaining reliable threat detection capabilities
- False positive management distinguishing between genuine threats and harmless signals
Integration and Remote Management
Modern security systems achieve maximum effectiveness through intelligent integration combining multiple technologies and enabling remote management:
- Centralized smartphone applications providing unified control and monitoring interfaces
- Intelligent alert filtering reducing notification fatigue while ensuring critical alerts reach you
- Redundant backup systems preventing single-point failures in critical security infrastructure
- Secure remote access enabling system adjustments and maintenance from anywhere
Professional maintenance protocols include regular battery replacement, equipment testing, software updates, security patches, and capability expansion as threats evolve or coverage requirements change.
System complexity requires the same methodical approach as network troubleshooting where systematic diagnosis and maintenance ensure reliable operation.
Future Technology Trends: Next-Generation Personal Security 🔮
Personal security technology continues evolving at breakneck pace with emerging technologies promising even more powerful capabilities at dramatically lower costs. Understanding future trends helps make intelligent long-term investments while avoiding obsolete technologies.
Artificial Intelligence and Machine Learning Integration
AI-powered security systems are rapidly becoming mainstream with capabilities that seemed like pure science fiction just years ago:
- Advanced facial recognition learning family members and trusted individuals while alerting to strangers
- Sophisticated behavioral analysis identifying suspicious activity patterns before threats materialize
- Voice recognition systems distinguishing between normal conversation and distress situations
- Predictive threat algorithms anticipating security problems before they occur
- Automated response systems taking protective actions without human intervention
Miniaturization and Power Efficiency Revolution
Surveillance devices continue shrinking dramatically while offering longer battery life and increasingly sophisticated functionality. Next-generation devices promise revolutionary capabilities:
- Ultra-miniature cameras smaller than current button cameras while recording in 8K resolution
- Solar-powered operation providing indefinite surveillance without battery maintenance
- Wireless charging compatibility enabling convenient power management without physical access
- Biodegradable surveillance devices for temporary monitoring applications
- Self-destruct capabilities protecting sensitive operations from discovery
Quantum Technology and Advanced Security
Quantum technology will revolutionize communication security and surveillance detection offering unprecedented capabilities:
- Quantum encryption providing mathematically unbreakable communication security
- Quantum radar systems detecting stealth surveillance devices impossible to find otherwise
- Quantum sensors with sensitivity and accuracy levels exceeding current technology
- Quantum networking creating completely secure device communication networks
- Quantum-resistant encryption protecting against future quantum computer threats
The future trajectory mirrors quantum computing development where revolutionary capabilities are becoming accessible to broader audiences.
Cost-Effective Security Solutions: Maximum Protection, Smart Budget Management 💰
Professional-grade personal security doesn’t require unlimited financial resources. Strategic purchasing decisions and intelligent technology selection provide excellent protection at reasonable costs, especially compared to traditional professional security services or potential losses from security breaches.
Entry-Level Professional Systems ($300-$800)
Foundational professional security can be established with carefully selected core equipment:
- Hidden Camera System: One high-quality smoke detector or clock camera ($200-$350)
- RF Detection Device: Effective professional bug detector ($100-$200)
- GPS Vehicle Tracker: For car and asset protection ($75-$150)
- Communication Security: Quality Faraday bag system for devices ($50-$100)
Total investment under $800 provides comprehensive foundational security coverage suitable for most personal protection needs while establishing upgrade pathways for future expansion.
Mid-Range Professional Systems ($800-$2,500)
Enhanced security capabilities justify moderate additional investment providing significantly improved protection:
- Multiple Camera Network: 3-4 strategically placed cameras with smartphone integration ($500-$800)
- Advanced Detection Equipment: Professional-grade RF/camera detection suite ($300-$500)
- Night Vision System: Digital night vision monocular or binocular system ($400-$700)
- Audio Surveillance Package: Professional voice recorders with remote capabilities ($200-$400)
- Enhanced Communication Security: Military-grade encrypted communication system ($150-$300)
Mid-range systems provide comprehensive coverage suitable for small business security or high-value residential protection while maintaining reasonable operational costs.
Professional-Grade Systems ($2,500-$8,000)
Serious security investments approach true professional capabilities rivaling commercial installations:
- Integrated Camera Network: 6-10 professional cameras with AI analytics and cloud storage ($1,000-$1,800)
- Advanced Detection Suite: Multiple specialized detectors for comprehensive threat sweeps ($600-$1,000)
- Thermal/Night Vision System: Professional fusion devices combining multiple imaging technologies ($1,000-$2,000)
- Comprehensive Audio Package: Multiple recording devices with directional capability ($500-$800)
- Advanced Communication Security: Encrypted radio systems and secure satellite messaging ($400-$800)
Professional-level systems rival commercial security installations while maintaining personal control, data privacy, and operational flexibility.
Return on Investment and Cost Justification
Security systems pay for themselves by preventing losses far exceeding system costs:
- Theft prevention value: Average residential burglary losses exceed $2,500, making security systems profitable after preventing single incidents
- Evidence collection benefits: Video evidence can determine successful prosecution versus total loss
- Insurance premium reductions: Many insurers offer significant discounts for comprehensive security systems
- Peace of mind value: Psychological security benefits prove difficult to quantify but enormously valuable
Investment analysis should consider long-term protection value similar to smart financial planning strategies focusing on preventing losses rather than just upfront costs.
Advanced Surveillance Techniques: Pro-Level Implementation 🎖️
Professional surveillance techniques separate effective security systems from amateur installations. These methods, used by law enforcement and security professionals, can be adapted for personal security while maintaining legal compliance and operational effectiveness.
Multi-Layer Surveillance Integration
Professional surveillance operations rarely rely on single technologies. Effective systems combine visual, audio, electronic, and physical security measures creating comprehensive protection networks:
Visual surveillance layers:
- Fixed hidden cameras for continuous area monitoring
- Mobile surveillance devices for flexible threat response
- Backup recording systems preventing evidence loss
- Remote viewing capabilities for immediate threat assessment
Audio surveillance integration:
- Ambient room monitoring for conversation capture
- Directional microphones for targeted audio collection
- Phone call recording for communication intelligence
- Audio enhancement systems for evidence clarity
Electronic countermeasures:
- Regular RF sweeps detecting hostile surveillance attempts
- Signal blocking during sensitive activities
- Communication encryption for operational security
- Electronic device monitoring for intrusion detection
Professional Operational Security
Operational security (OPSEC) principles protect your surveillance capabilities from discovery and compromise:
- Need-to-know information sharing: Limiting knowledge of your security systems
- Technology rotation: Regularly changing devices and locations
- Counter-surveillance awareness: Monitoring for surveillance of your activities
- Evidence security: Protecting recorded material from theft or destruction
- Legal compliance maintenance: Ensuring all activities remain within legal boundaries
Professional deployment requires understanding both offensive and defensive aspects of surveillance technology. Protecting your systems from discovery while maximizing their effectiveness against threats demands systematic operational planning.
The complexity of professional security operations mirrors enterprise cloud security where multiple technologies must coordinate effectively while maintaining security.
Cutting-Edge Innovation: What’s Coming Next in Personal Security 🚀
Revolutionary technologies currently in development will transform personal security capabilities within the next few years. Understanding these emerging trends helps make forward-looking investment decisions and prepare for rapidly evolving threat landscapes.
Augmented Reality Security Systems
AR technology will transform how we interact with security systems and respond to threats:
- Real-time threat overlays visible through smart glasses showing security status
- Interactive security management through gesture control and voice commands
- Virtual security guard assistance providing 24/7 expert monitoring support
- Immersive training systems for learning security device operation and emergency procedures
- Predictive threat visualization showing potential security vulnerabilities before incidents
Advanced AI and Automation
Next-generation AI systems will provide unprecedented automation and threat prediction capabilities:
- Behavioral prediction algorithms identifying potential threats before suspicious activity begins
- Automated response systems taking protective actions without human intervention
- Cross-platform integration coordinating security devices from different manufacturers
- Learning threat recognition adapting to new attack methods and surveillance techniques
- Emotional state analysis detecting stress, deception, or aggressive behavior through video analysis
Quantum-Enhanced Security Technology
Quantum technology applications will eventually provide ultimate security capabilities:
- Quantum-encrypted communications offering mathematically unbreakable security
- Quantum sensing technology with unprecedented detection sensitivity and accuracy
- Quantum radar systems capable of detecting previously undetectable stealth devices
- Quantum-resistant encryption protecting against future quantum computer attacks
Future security technology development parallels AI advancement trends where revolutionary capabilities become accessible to broader user bases.
Real-World Implementation: Success Stories and Case Studies 📋
Professional-grade personal security systems have prevented countless crimes, protected vulnerable individuals, and provided crucial evidence in legal proceedings. These real-world applications demonstrate the practical value and effectiveness of modern surveillance technology.
Home Security Success Stories
Hidden camera systems have documented break-ins leading to arrests, identified package thieves, caught abusive caregivers, and provided crucial evidence in insurance claims. Modern systems’ smartphone integration enables immediate police notification and real-time evidence sharing.
Counter-surveillance detection has revealed unauthorized monitoring in private homes, located GPS trackers placed by stalkers, identified listening devices in sensitive business meetings, and uncovered corporate espionage attempts.
Business and Professional Applications
Workplace surveillance systems have documented harassment cases, prevented theft of intellectual property, identified security breaches, and provided evidence for legal proceedings. Professional-grade systems offer evidence quality meeting legal standards for court proceedings.
Mobile surveillance has protected traveling executives, documented service quality issues, identified fraudulent business practices, and provided security for high-value transactions.
Personal Protection Applications
Individual security systems have prevented stalking incidents, protected children from predators, monitored elderly relatives’ safety, and provided evidence in domestic abuse cases. Modern technology’s accessibility enables ordinary people to access protection previously available only to wealthy individuals or corporations.
Vehicle security systems have recovered stolen cars, identified hit-and-run drivers, prevented carjacking attempts, and monitored teenage driver safety. GPS tracking combined with camera systems provides comprehensive vehicle protection.
Real-world success demonstrates the same practical value as proven technology solutions where proper implementation generates significant benefits.
Emergency Response Integration: When Security Systems Save Lives 🚑
Modern security systems increasingly integrate with emergency response services, providing automated threat detection and immediate professional assistance when personal safety is threatened.
Automated Emergency Response
AI-powered threat detection can automatically contact police, fire departments, or medical services when specific threat patterns are identified:
- Intrusion detection triggering immediate police notification with live video feeds
- Medical emergency recognition through behavioral analysis or biometric monitoring
- Fire and smoke detection with automatic fire department notification
- Panic button integration for immediate help summoning during personal attacks
- Geofencing alerts notifying emergency contacts when individuals enter dangerous areas
Professional Monitoring Integration
Security monitoring services provide 24/7 professional oversight of personal security systems with trained operators responding to threats:
- Live video verification confirming threats before emergency service dispatch
- Two-way communication allowing operators to assess situations and provide guidance
- Multiple contact protocols ensuring help reaches you through various communication methods
- Legal compliance management ensuring evidence collection meets legal standards
- Coordinated response planning with local law enforcement and emergency services
Personal Safety Networks
Modern security systems create personal safety networks connecting family members, trusted friends, and professional services:
- Automated check-in systems ensuring regular safety confirmations
- Location sharing protocols for family safety monitoring
- Emergency escalation procedures when primary contacts are unavailable
- Medical information integration for emergency responders
- Threat intelligence sharing within trusted networks
Emergency integration reflects the same comprehensive approach needed for disaster recovery planning where preparation and automation save critical time during crises.
Conclusion: Taking Control of Your Security Destiny in 2025 🎯
The world has fundamentally changed, and your security strategy must evolve accordingly. The sophisticated surveillance technology once exclusive to government agencies and wealthy corporations is now accessible to anyone serious about protecting themselves, their families, and their assets. But with this incredible power comes significant responsibility – and unprecedented opportunity.
Here’s the bottom line: The spy gadgets for personal security market will continue its explosive growth trajectory, reaching $2.45 billion by 2032. This growth doesn’t just reflect technological advancement – it represents genuine, widespread need. Privacy violations, surveillance threats, and personal security concerns affect millions of people daily across all demographic groups and income levels.
You face a critical choice. You can continue hoping that security threats will somehow pass you by, relying on luck and the goodwill of others, or you can take control using proven professional-grade security technology that puts protective power directly in your hands.
Start implementing protection today. Begin with fundamental detection equipment and one hidden camera system. Learn how the technology operates. Understand your local legal requirements. Build practical skills and operational confidence. Then systematically expand your security capabilities as threats evolve and budget allows.
Professional-grade spy gadgets for personal security represent more than just clever gadgets – they’re essential survival tools for navigating our increasingly monitored and dangerous modern world. A comprehensive personal security system costs less than most people spend on entertainment or dining out annually, yet provides protection that could literally save your life, protect your family, or preserve your livelihood.
The technology exists. The threats are real. The choice is entirely yours.
Whether you’re protecting your home from intruders, your business from corporate espionage, your family from stalkers, or yourself from workplace harassment, professional surveillance technology provides capabilities that were completely unimaginable just decades ago. These powerful tools must be used responsibly, legally, and ethically – but they work.
Just as cloud technology democratized access to enterprise-grade computing power, modern spy gadgets have democratized access to professional security capabilities. The question isn’t whether you need personal security technology in 2025 – the question is whether you’re prepared to take advantage of it before you desperately need it.
Your security remains your responsibility. These advanced tools make that responsibility manageable, effective, and affordable. The rest depends entirely on your willingness to act. In a world where privacy is under constant attack and personal security threats multiply daily, professional spy gadgets for personal security aren’t luxury purchases – they’re essential survival equipment for thriving in the modern world.
Take control. Protect what matters. Start today.